6 min read
The Hidden Security Risks of External Scanners on Key Cabinets
Shannon Arnold : April 16, 2026
Verifying Transactions: The Blind Spot Using External Scanning for Authentication
Many key management systems on the market tout the convenience of their External scanner verification. Its main selling point is its ease of use for key check-out and check-in. However, emphasizing convenience overlooks a fundamental security limitation in systems that rely solely on RFID scanning outside the key cabinet system: You don’t actually have verification that keys are returned.
At ecos, we call this the ‘verification gap,’ and it can be a critical blind spot in key management.
When a user returns a key in a system that uses external scanning, they present an RFID tag to an external scanner mounted near the key cabinet. The RFID tag is typically attached to the key fob. The system reads the tag, and the software confirms the key is returned.
But the key isn’t actually in the cabinet yet.
The Verification Gap Prevents Accountability
The system only verified that the key fob was present. It has no way to confirm whether the physical key was returned to its slot. This is particularly problematic when dealing with sensitive keys, such as master keys, or in high-security environments.
A disgruntled employee, another bad actor, or a forgetful employee could present the key fob to the reader and then fail to return the key. Your verification gap has left you with a breakdown in the key management responsibility: accountability.
If the system cannot confirm the key's physical presence in the cabinet, your audit trail has broken down. You’re leaving your organization exposed to potential risks ranging from simple work delays while time is spent hunting down a missing key to fraud or industrial espionage.
Real-World Security Implications
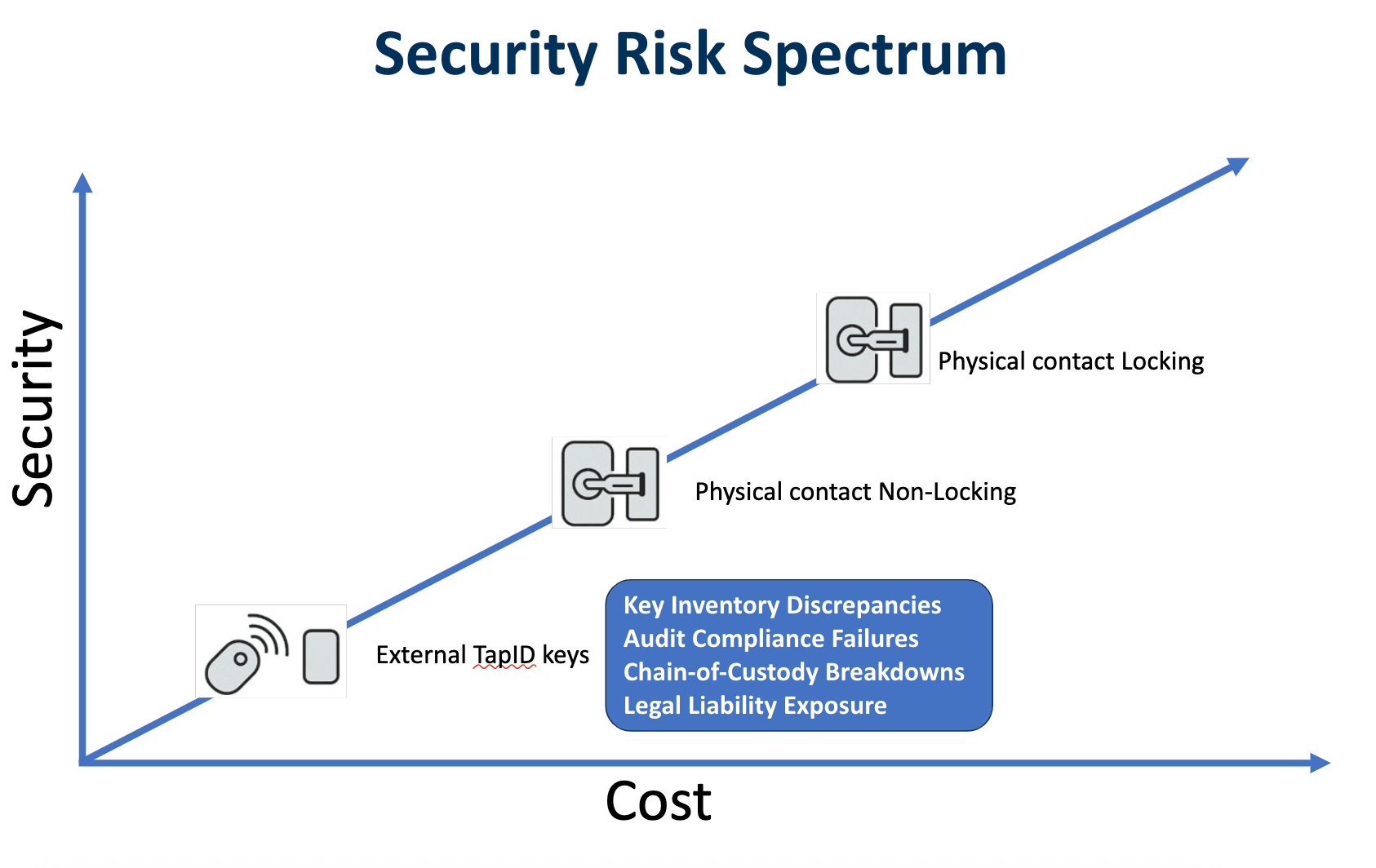
While the convenience of external scanning (or Tap ID) is very appealing, every user organization needs to ask itself, “Is it worth it?” Consider the practical security implications of this verification gap.
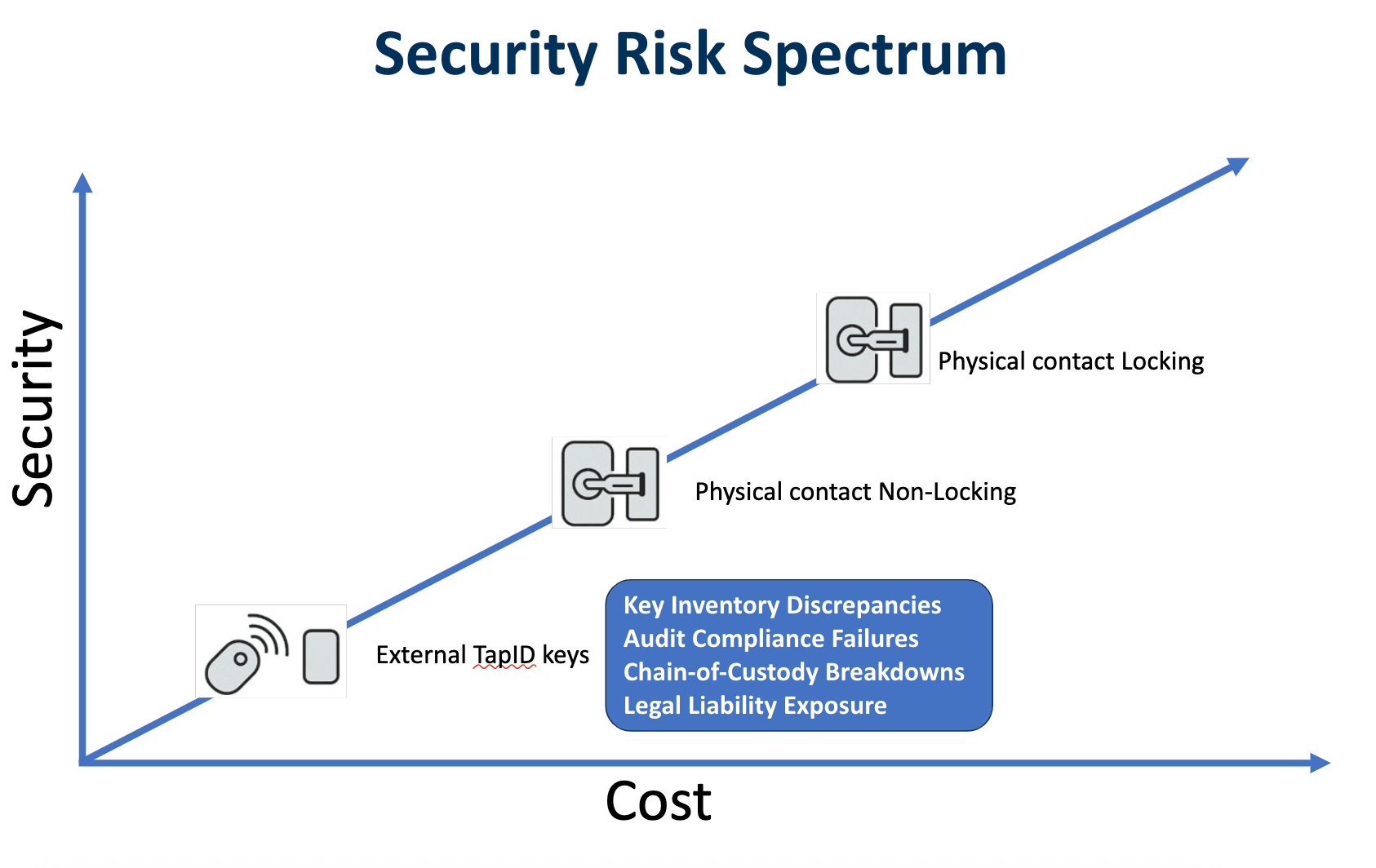
- Key Inventory Discrepancies: Because these systems cannot confirm the physical return of keys, it’s just a matter of time before your key system records a missing key as present. As these discrepancies build up, operations will suffer, and your ability to manage emergencies could be impaired.
- Audit Compliance Failures: During security reviews or audits, unreliable key tracking can lead to compliance issues.
- Chain-of-Custody Breakdowns: A clear chain of custody is essential in sensitive environments, such as where workers handle confidential information or hazardous materials. If your facility or assets are sensitive, you must treat the keys that grant access as sensitive.
- Legal Liability Exposure: Your organization could face legal liability if certain sensitive keys are misrepresented as secure. For example, if a security breach occurs and it's discovered that the key management system provided inaccurate information about key access, the organization could be held legally responsible for losses and violations.
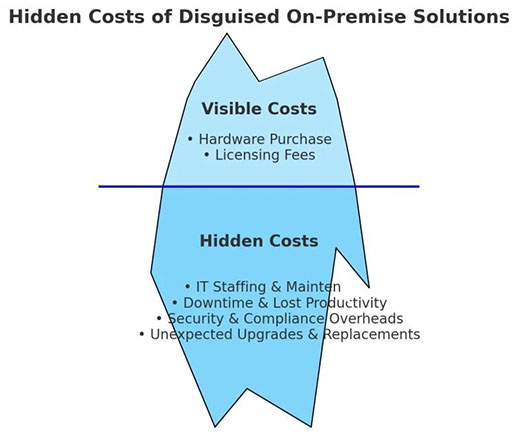
The Hidden Costs of Key Security
When evaluating key management systems, most buyers want to start by comparing the initial purchase price. This is understandable, of course. However, for a ‘live’ business management system, return-on-investment (ROI) is a much better way to compare costs, especially an ROI framework that considers the value of risk mitigation.
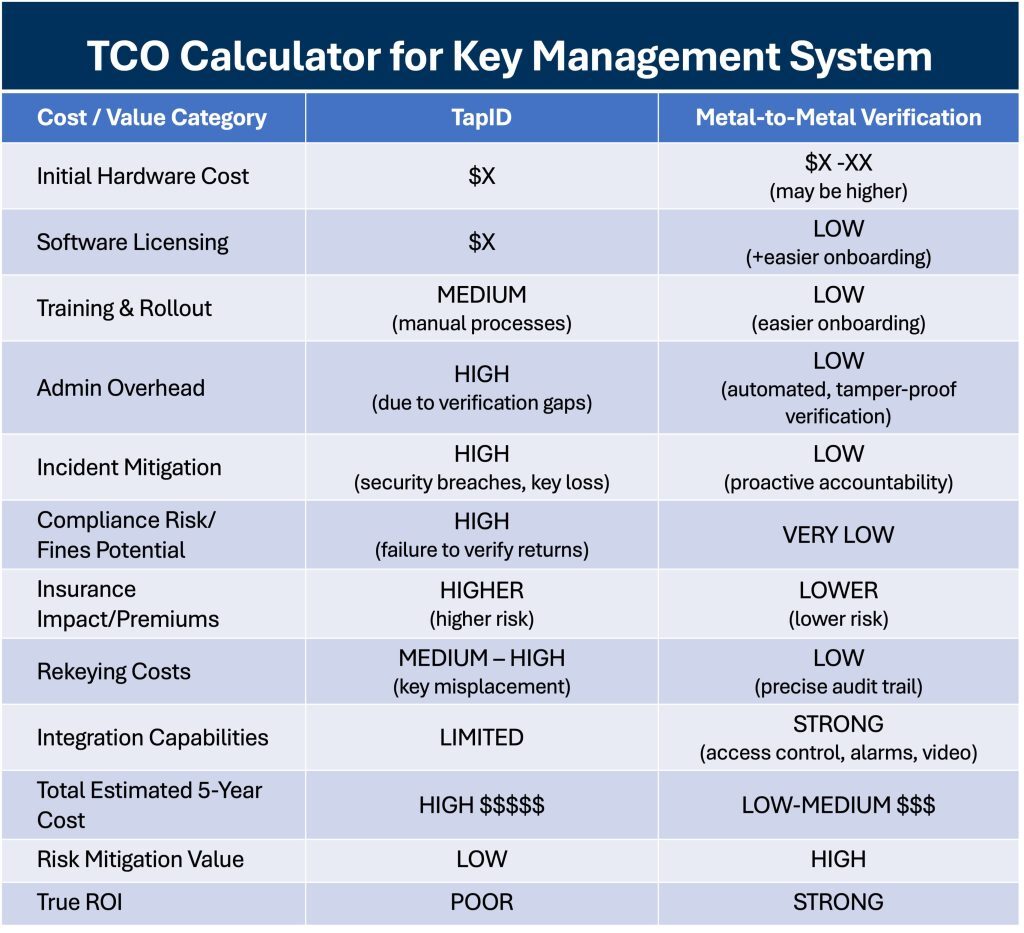
Here are some potential hidden costs to consider:
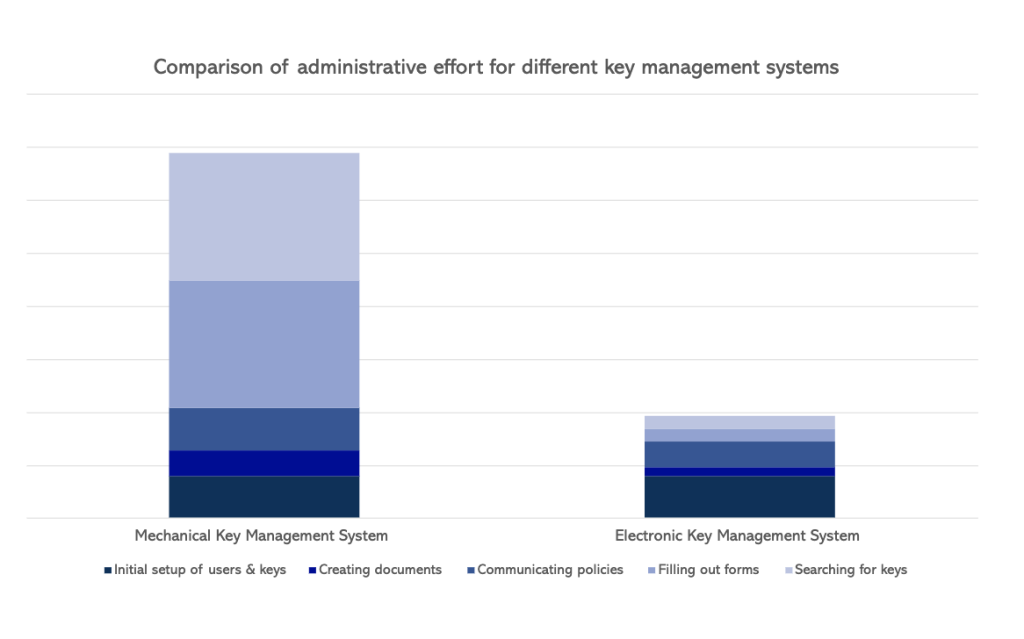
- Administrative Overhead: If your key system cannot provide reliable physical verification, your staff will inevitably need to compensate with manual procedures, such as physical audits, redundant manual logging, and unnecessary investigations into missing keys.
- Costs of Security Incidents: Security breaches are costly. There are investigations, repairs, and potential regulatory fines and legal fees to consider. There’s lost productivity on top of all that, while staff redirect work hours to managing the incident. The financial impact can be significant if a key loss results in a security breach.
- Potential Regulatory Fines: To drill deeper here, inaccurate key tracking can lead to failures during audits in industries with strict regulatory compliance requirements. Notably, HIPAA and PCI DSS require strong physical protection of hard copy personal data and the IT infrastructure on which it’s stored. If your system cannot prove the secure return of critical keys, you risk non-compliance.
- Insurance Premium Implications: Insurance providers may view key systems with known security limitations as higher risk. This could lead to increased insurance premiums or even affect your ability to obtain coverage for certain losses.
- Rekeying Costs: When keys are genuinely lost, but the system incorrectly indicates they were returned, the organization may incur high rekeying costs to secure entire facilities or critical areas.
So, while initial price points may appear similar between two products on first examination, upon deeper analysis, in most situations, systems with robust physical verification, such as ecos systems' metal-to-metal contact verification, can have a significantly higher ROI in the long run.
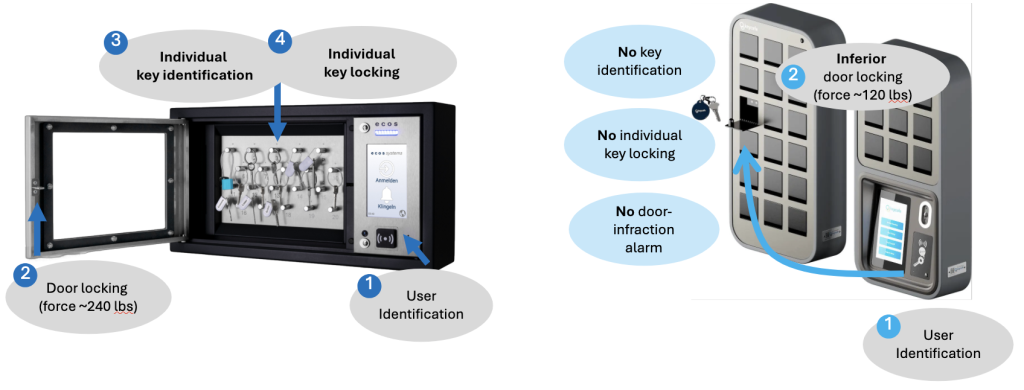
Technical Comparison: External Scanning vs. Physical Verification
Let’s dive deeper into the differences between external scanning and metal-to-metal key verification.
External RFID Scanning (Tap ID): Verification by Proximity
As discussed earlier, these systems rely on Radio-Frequency Identification (RFID), a short-range wireless standard commonly used for automated, asset-to-system communication, such as verifying the presence of a tag at a scanner. When an RFID tag attached to a key fob is brought within range of an RFID scanner on the key cabinet, the scanner reads the tag's unique identifier. The system then registers the associated key as "returned."
But as we’ve already pointed out, the system has only verified the presence of the RFID tag near the scanner. It has not confirmed the physical presence of the key secured inside the cabinet.
Physical Contact Verification (Metal-to-Metal Contact): Verification by Presence
In contrast, ecos and similar key systems utilize metal-to-metal contact verification, also known as verification by presence. Key fobs with metal contact plates securely dock within a dedicated port inside the key cabinet. Metal-to-metal contact allows them to complete an electrical circuit and verify that keys are in the cabinet.
Tampering Resistance Comparison
RFID tags used in external scanning systems can be relatively easily detached from the key, duplicated, or even simulated. This further increases the risk of "phantom returns" and undermines system integrity. In contrast, metal-to-metal contact verification requires a direct physical connection between the key fob and the secure locking port, making tampering significantly more difficult.
What to Consider When Selecting a Key Management System
There are three pillars to a successful key management program: technology, policies, and training. Evaluate all key systems you consider against your needs in all three areas—first, the technology.
How to Evaluate Key System Technology
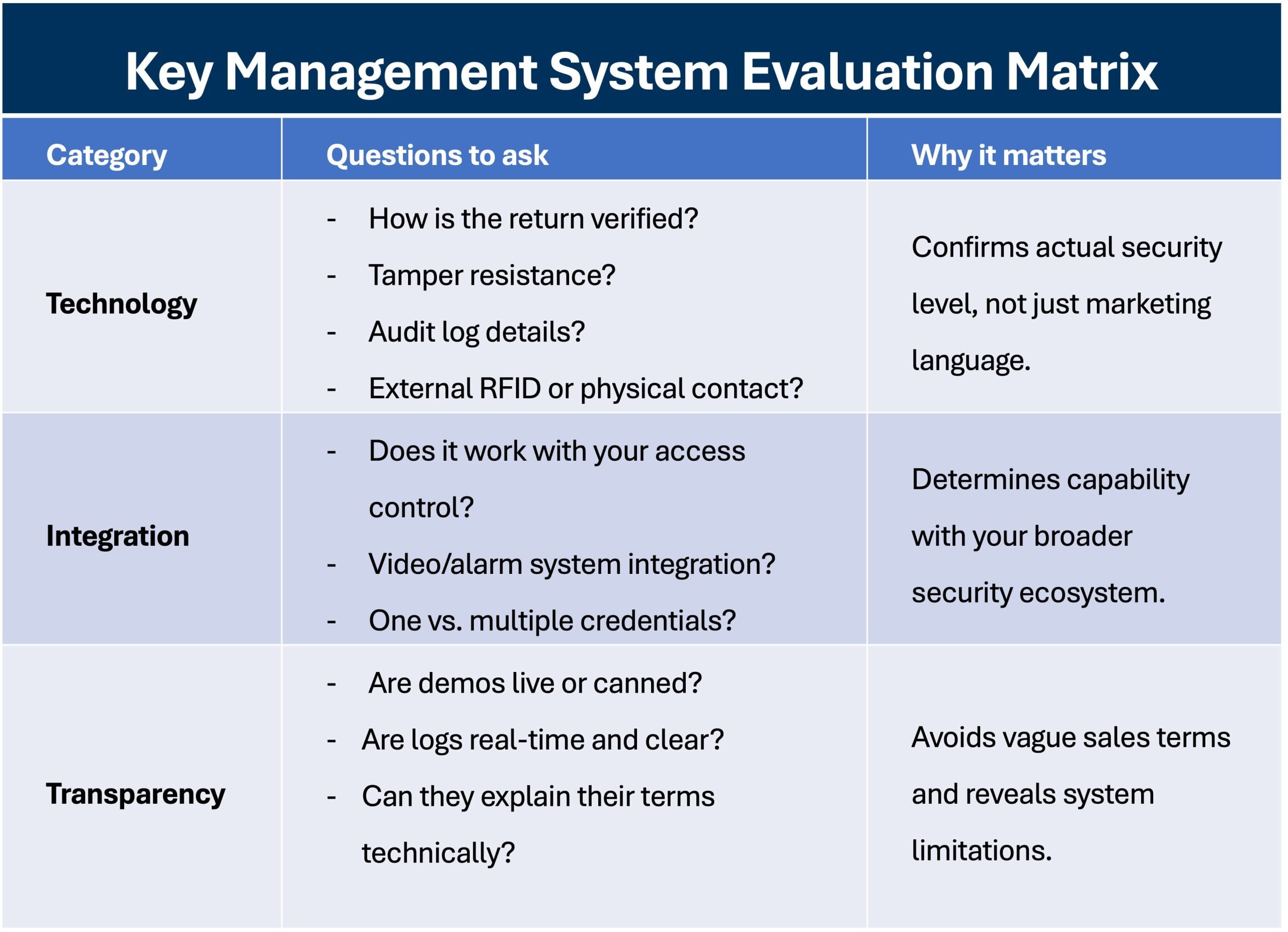
All too often, key system salespeople and marketing material will say their product has electronic verification and leave it at that. If you’re serious about purchasing a key management system, you should insist on digging deeper.
Here are some practical steps every buying organization should take when evaluating which key management system is best for their facility:
Questions to Ask Manufacturers About Return Verification
- "What tamper protection does your key system offer for verification?"
- "How does your system verify keys are physically returned to the cabinet?"
- "Does your system solely rely on any method other than external RFID scanning to verify returns?"
- "What mechanisms are in place to prevent 'phantom returns?’"
Skip the Marketing Talk and Get Details
Review Audit Logs: Request to view sample audit logs to better understand the level of detail provided for key returns. Does the system record a tag scan or confirm a physical docking or latching?
Start with Physical Security: Skip the buzzwords and evaluate the technical specifications. Of course, check the key verification method. But has the key system been designed to meet any specific industry specifications for tamper resistance? Additionally, consider the locking mechanisms and how you might position the cabinet within your facility. Different products might be more or less secure depending on where you want to place them.
Insist on Getting Technical Details: "Secure" or "auditable" are common terms in key system marketing language, but they’re vague. How secure? How auditable? See technical specifications for software security features and details on tracking and logging capabilities.
Get Live Demos: Recorded demos are helpful, but today most vendors can provide live demos via video call. Ask to see the specific functions your organization needs.
Assess Your Integration Needs
Alarm System Integration: In some high-security environments, integrating your key cabinet with your alarms can be very beneficial. If there is a security issue, your entire team can receive automated alerts from the key system.
Access Control Integration: This is usually the most important aspect for most organizations to review. Which of the key management systems you’re considering can integrate with your access controls? Are you using a swipe card for building entry? Will that work with the key system, or will users need to carry a second form of identification just to get keys?
Video Surveillance Integration: High-security settings might benefit from integrating video surveillance with their key system. For example, adding a camera near your key cabinet provides an added layer of accountability. Will the systems integrate so that you capture the footage you want? If not, consider choosing a key management system with integrated cameras.
Evaluate How Key Management Systems Fit With Current Policies
Buying a new key management system can improve key security, but if you don’t combine it with proper guidance and procedures, you won’t get as much from your investment as possible. That’s why the second pillar of a good key management program is policy.
Conduct Regular Policy Reviews: Periodically review and update your key management policies to reflect any changes in your security requirements that might have arisen within your organization.
Roles and Responsibilities: You’ll need to clearly define the roles and responsibilities for individuals authorized to access keys, as well as for system administrators, including proper user creation and access privilege update processes.
Key Handling Procedures: Develop comprehensive policies outlining the proper procedures for checking out, using, and returning keys. This is your bread and butter.
What Key Security Training Will You Need to Conduct?
The third and final pillar is training. Your investment in a key system will be wasted if your people don’t know how to use it in the real world. How easy is each product for your staff to use out of the box? Will you need to conduct a rolling deployment because it requires comprehensive training? Or can your staff use it on day one?
Take Control of Your Key Security & Request a Personalized Assessment From ecos
Are you worried about gaps in your key security? Need more automated control and better accountability? Don't wait for a security incident to expose the risks in your current key management processes. Request a personalized assessment from ecos systems specialists today.
During your call, our experts will:
- Answer all your questions about establishing a secure and accountable key management solution.
- Discuss your current key management practices and identify potential security gaps.
- Provide a personalized risk assessment tailored to your unique operational environment.
Sign up
Receive an email when we publish new articles.