Fleet Management Apps vs. Fleet Key Management Solutions
Fleet management apps have been a popular solution with fleet managers for years. No wonder they are so effective. Driver input and telematics can...
6 min read
Shannon Arnold : Updated on April 24, 2026

You might have bleeding-edge cybersecurity ready to pounce on any threat coming over the Internet, but that means nothing if attackers can just gain direct access to systems through unsecured doors, keys, or devices.
The reality today is you can’t think of security as physical or cyber. They’re converging. Digital breaches can provide physical access, and lapses in physical security can compromise systems. Good organizational security requires defending both fronts.
And for organizations managing power grids, water treatment plants, transportation hubs, and other critical infrastructure, the stakes couldn’t be higher. A breach doesn’t represent just a potential data leak; it can mean service outages across entire regions, public safety risks, or even national security risks.
This article examines how modern threats can exploit weak physical access controls, equipment security, and key management. And how intelligent access systems like ecos provide verifiable, auditable control over who enters your most sensitive spaces.
Today’s adversaries—nation-states, hacktivists, and organized crime—continue to exploit gaps in the convergence of physical and network security measures.
The 2021 ransomware attack on Colonial Pipeline made it clear to everyone that a single, unsecured account is all it takes to trigger an incident that forces 17 US states to declare a state of emergency. Hackers gained access via a compromised password for an old, unused virtual private network (VPN) account that the employee no longer needed for remote access.
Since then, the Cybersecurity and Infrastructure Security Agency (CISA) has emphasized that protecting operational technology (OT) environments requires both rigorous “digital hygiene” and robust physical access controls as a foundational layer of security. You can’t rely on just one or the other.
According to CISA intelligence reports, nation-state actors—including those from China, Russia, and Iran—are actively mapping vulnerabilities in U.S. and European critical infrastructure. Their tactics include:
Intentionally or unintentionally, your employees and contractors with legitimate physical access can become attack vectors. A disgruntled worker with late-night access or a vendor technician with elevated privileges can bypass both digital and procedural safeguards. This isn’t a hypothetical threat either. Within the past year, CISA has warned critical infrastructure organizations about efforts by PRC-sponsored hacking groups to identify systems and individuals vulnerable to compromise.
While critical infrastructure organizations invest millions in network security, attackers increasingly look to bypass those measures entirely by switching to physical attack vectors. A stolen badge, a rogue USB drive or laptop smuggled into your facility, or an unverified contractor can potentially do more damage than any phishing campaign.
The Stuxnet worm, widely believed to have been delivered via a planted USB stick, targeted industrial control systems at Iran’s Natanz nuclear facility. No network vulnerability was needed—just physical access.
The USB drop can be one of the most effective and low-tech attack methods available. An attacker leaves infected drives in parking lots, lobbies, or break rooms. Curious employees plug them in, unknowingly executing malware.
As an aside, ecos equipment management systems can include automated drawers that close after use to prevent unauthorized access to organizational USB devices. The system’s software dashboard and associated ecos webman mobile app also help you inventory and track them.
Other common physical-to-digital attack methods include:
Attackers will seek the weakest links to exploit. If they want to target workers, they’ll likely consider how to exploit contractors and 3rd-party service workers, who often have less rigorous vetting and security training.
Consider whether your organization might have any of these common vulnerabilities:
These “temporary” privileges can easily become long-term liabilities.
Traditional key management systems offer little protection against duplication. Metal keys can be copied at any hardware store. Plastic fobs and RFID cards can be cloned with inexpensive tools. If your key management lacks audit trails, you’ll rarely know when it happens.
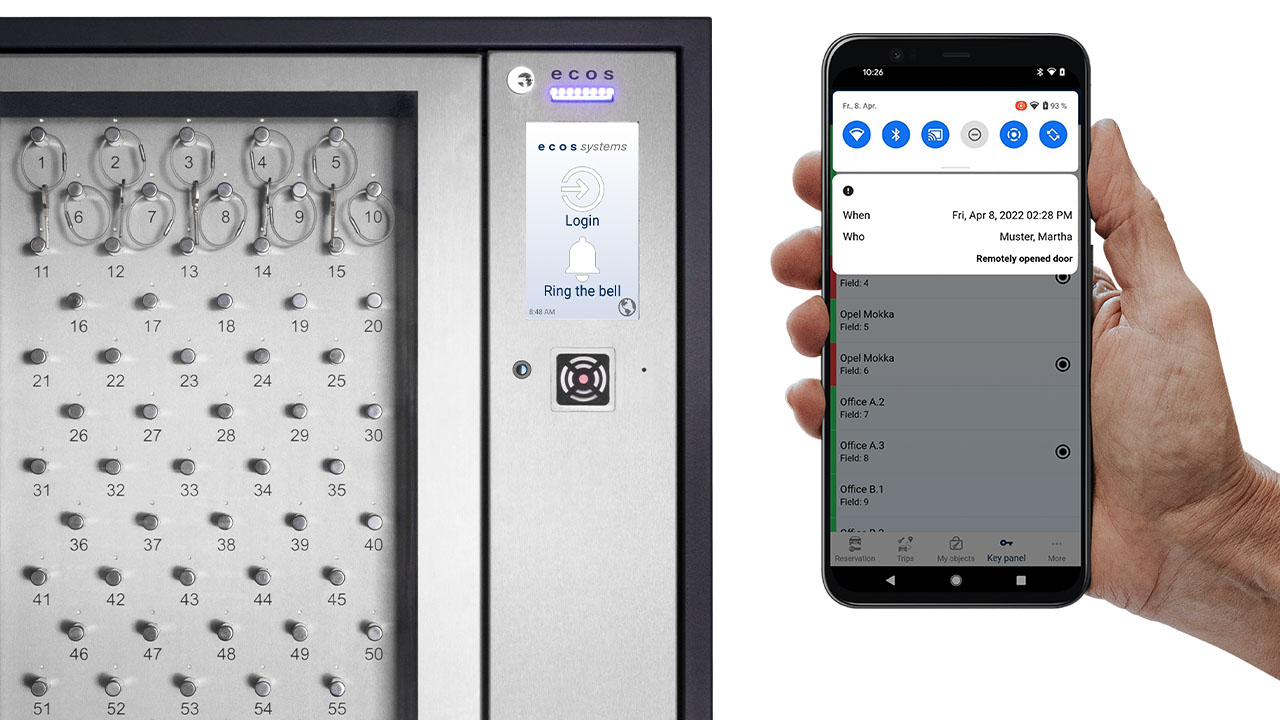
Key management systems that include integrated cameras act as an additional layer of security against unauthorized access. For example, ecos systems include an integrated camera that can capture pictures or videos of users at the cabinet. This allows various use cases from real-time verification of a user’s ID card to investigation purposes in case of a security event.
Global security frameworks have long recognized the importance of converging physical security with cybersecurity. For example, standards such as KRITIS (Germany’s critical infrastructure regulations), ISO/IEC 27001 (internationally), and CISA guidelines in the US all mandate physical security controls.
Meet multiple standards with one system
The strength of a modern access control platform lies in its ability to satisfy multiple regulatory regimes simultaneously. Rather than implementing separate systems for different standards, organizations using modern key management systems, like those from ecos, can achieve unified compliance.
Modern security architecture should use your physical access controls as a real-time, intelligence-driven layer of defense. This means moving to systems that monitor, analyze, and respond to access events the moment they occur.
ecos delivers this next-generation approach—designed for the realities of 24/7 operations, regulatory scrutiny, and converged cyber-physical threats.
Most traditional key management systems operate on a batch communication model. Data is collected locally and uploaded once a day, or even once a week. That delay creates dangerous blind spots.
ecos systems use their continuous 4G/5G connectivity to provide real-time updates on all key transactions through our ecos care service. This is independent of your local IT network. Even if someone removes a key at, say, 2:17 a.m., the system alerts supervisors instantly.
More importantly, ecos can automatically identify and alert on anomalies:
ecos automates compliance with real-time, GPS-tagged logs that tell you who accessed which keys, where, and when. Reports are generated on-demand or scheduled automatically—ensuring you meet strict timelines like those required under KRITIS or CISA guidelines. And because all data is cloud-synced and backed up via ecos care, your records are safe even if local power or network service fails.
With ecos systems, you can issue temporary credentials to contractors and visitors before they even arrive on site through the ecos webman mobile app. Access is limited by time, location, and purpose. You can use asset lockers to provide temporary, secure storage for laptops, USB drives, and other digital devices that might compromise your network once they enter your perimeter. And you can set an automatic expiration date so stale credentials never create vulnerabilities.
Basic access cards or PINs are easy to lose, steal, or share. ecos supports several multi-factor authentication modes, including:
Even stronger is multi-user authentication—a rare capability among smart key management systems. For high-security keys, you follow the well-established “two-person rule,” requiring two authorized personnel to be physically present to unlock the key. Unlike competitors who treat this as an add-on feature or not at all, ecos builds it into their core key management system.
As we’ve seen, the most effective security strategies no longer treat physical and cyber defenses as separate. Attackers are actively seeking ways to exploit one domain to access another. Your security measures need to stop them in both.
ecos key management systems are built for this integrated reality. They help you seamlessly coordinate between physical access control and cybersecurity operations. The goal is to help you move from merely reactive measures to fully proactive security.
When an ecos key cabinet detects suspicious behavior, it sends real-time alerts to designated personnel via email, SMS, or push notification. Supervisors can review the event, verify identity, and take action when needed. And they can do all this anywhere in the field from the ecos webman mobile app.
ecos care includes a 24/7 telephone hotline staffed by trained technical support specialists. No other key management provider offers this round-the-clock support. Most rely on email tickets or business-hour help desks. That lag time for off-hour emergencies can put lives at risk when you’re managing critical infrastructure.
Resilience means being ready when things go wrong. Even during a power failure or when you suffer connectivity loss, your ecos system stays online and functional.
You can’t prevent every threat to your infrastructure. But you can build a system that detects risks early, responds faster, and recovers with confidence.
Physical access is your first line of defense. Make sure it’s built to last.
Schedule a consultation with ecos key management specialists today.
Fleet management apps have been a popular solution with fleet managers for years. No wonder they are so effective. Driver input and telematics can...

You might have bleeding-edge cybersecurity ready to pounce on any threat coming over the Internet, but that means nothing if attackers can just gain...