Critical Infrastructure Security Begins With Asset Accountability
You might have bleeding-edge cybersecurity ready to pounce on any threat coming over the Internet, but that means nothing if attackers can just gain...
6 min read
Shannon Arnold : Updated on April 24, 2026
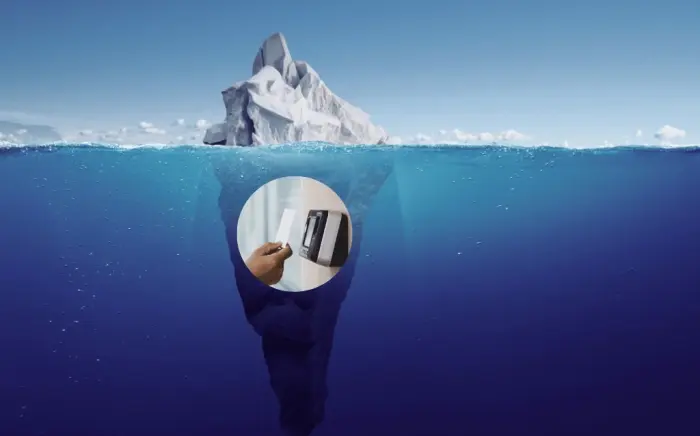
Modern smart asset management systems often use external scanning to verify device sign-in and sign-out. Providers of these systems will tout their convenience and reliability. But that focus ignores a fundamental limitation of external verification: you don’t actually have verification that the device was returned.
Let’s walk through the process.
When someone returns a device to an asset management system using external scanning, they present the device’s radiofrequency identification (RFID) tag to an external scanner, which is typically mounted on or near the system. The scanner reads the tagged asset and logs it as returned.
But the device isn’t secured yet. The user just verified it's near the storage system.
At ecos, we call this the ‘verification gap,’ and it is often a critical blind spot in equipment and device management.
A system with external scanning can only verify that a device is present with the user near the management system at the time of authentication. It has no way to verify that the device was actually secured. This control gap can be a serious concern if you’re managing mission-critical or expensive equipment.
A disgruntled or malicious employee, or even just a forgetful one, could log a device returned at your scanner and then fail to return it to storage. The verification gap could leave your organization exposed to a range of issues:
Bridging this gap often requires significant manual management, something you were probably hoping to avoid by procuring an automated smart management system.
It’s hard to deny the convenience of external scanning. Still, if you’re considering purchasing a smart asset management system for your organization, it’s worth thinking about whether that convenience is worth the security risk. First, consider all of the real-world smart locker security implications you might face.
Most buyers want to start with an initial purchase price when evaluating asset management systems. This is understandable, but smart management systems are better approached as live, evolving services that will adapt with your organization over time. Therefore, return on investment (ROI) is a more suitable metric, especially an ROI framework that accounts for the indirect costs mitigated by effective asset management practices.
Here are some potential hidden costs to consider:
So, you can compare two products that you think are at similar price points. But a little bit of investigation will often reveal that systems with robust physical verification, such as ecos systems' internal verification methods, will have a better ROI in the long run.
Let’s dive deeper into the differences between external scanning and physical verification.
As discussed at the outset, these systems rely on RFID scanning, a short-range wireless standard commonly used for automated machine-to-machine communication. In our case, we verify the presence of an asset tag at a scanner outside the storage system.
When a user presents a device with an attached RFID tag at the RFID scanner on the management system, the scanner reads the tag's ID and registers the device as "returned." But as we’ve pointed out, the system has only verified the presence of the RFID tag near the scanner. It has not been verified that the device is secured within the locker system. In other words, it’s verification by proximity only.
In contrast, ecos smart lockers operate on the principle of verification by presence. An asset isn’t verified returned until RFID sensors inside the flooring of the locker compartments confirm it’s secured in the locker system. In other words, unlike external scanners, ecosverifies the presence of an RFID tag within a locker compartment. The system won’t let the user complete a transaction unless they actually take or return the asset, ensuring 100 percent security. These ecos sensors are fast-acting, so a quick signout-and-grab transaction is fully recorded. All tracking and management run in the background, so your users never have to think about it.
There are three pillars of a good asset management program you must assemble: your technology, your policies, and your training. Evaluate every asset management system on your shortlist against your needs in these three areas.
First, your technology.
If you’re serious about purchasing an asset management system, you should push beyond surface claims that a product offers electronic verification. How does it verify? What technologies? What process?
Here are some practical steps every buying organization should take when evaluating which asset management system is best for their facility:
Assess Integration Needs
Get Specifics
The second pillar of a good asset management program is policy. Combining the purchase of an asset management system with reliable policies prescribing its use will help you get the most out of your investment.
The third and final pillar is training. Remember, you should think in terms of ROI, as purchasing an asset management system is an investment in both security and productivity. That investment will go to waste if your people don’t know how to use it. Evaluate how easy each system is to use out of the box. What functions can staff perform without training? What essential functions will need formal training?
Are you worried about security gaps in your assets? Do you need more automated control and better accountability? Don't wait for a security incident to expose the risks in your current asset management processes. Request a personalized assessment from ecos systems specialists today.
During your call, our experts will:

You might have bleeding-edge cybersecurity ready to pounce on any threat coming over the Internet, but that means nothing if attackers can just gain...